Unknown Facts About Risk Management Enterprise
Table of ContentsThe Facts About Risk Management Enterprise RevealedSome Known Incorrect Statements About Risk Management Enterprise Top Guidelines Of Risk Management EnterpriseThe Ultimate Guide To Risk Management EnterpriseNot known Details About Risk Management Enterprise Fascination About Risk Management EnterpriseThe 10-Minute Rule for Risk Management Enterprise
Real-Time Risk Analyses and Mitigation in this software allow companies to constantly check and review dangers as they evolve. When dangers are identified, the software program facilitates prompt mitigation activities.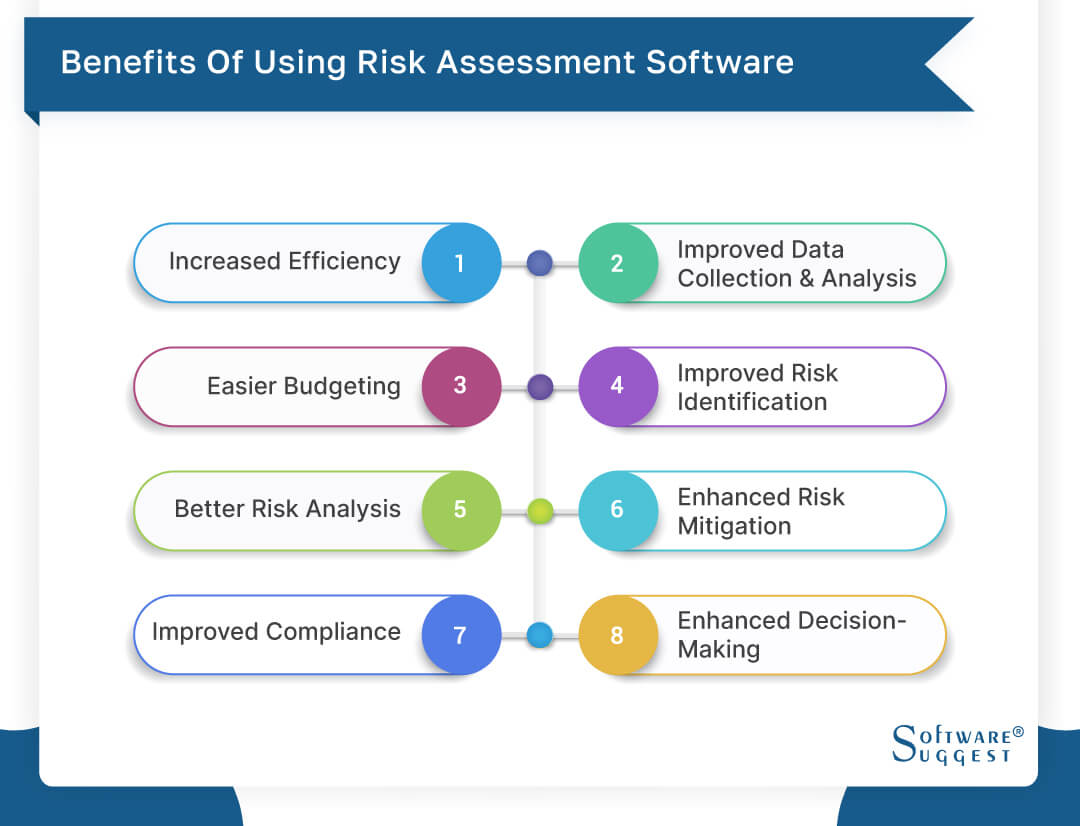
They deal with the obstacle of ongoing danger administration by offering tools to keep track of threats continuously. KRIs enhance security risk oversight, making sure that potential risks are determined and taken care of effectively.
Risk Management Enterprise Fundamentals Explained
IT run the risk of monitoring is a part of enterprise risk administration (ERM), made to bring IT run the risk of according to a company's threat appetite. IT risk management (ITRM) incorporates the plans, treatments and modern technology necessary to minimize dangers and vulnerabilities, while preserving conformity with suitable regulatory demands. On top of that, ITRM looks for to limit the consequences of damaging events, such as safety and security breaches.
Veronica Rose, ISACA board director and an information systems auditor at Metropol Corp. The ISACA Threat IT framework aligns well with the COBIT 2019 structure, Rose claimed.
Business Threat Administration Software Application Growth: Advantages & Features, Expense. With technical developments, risks are constantly on the surge., companies browse via a constantly changing sea of dangers.
Excitement About Risk Management Enterprise
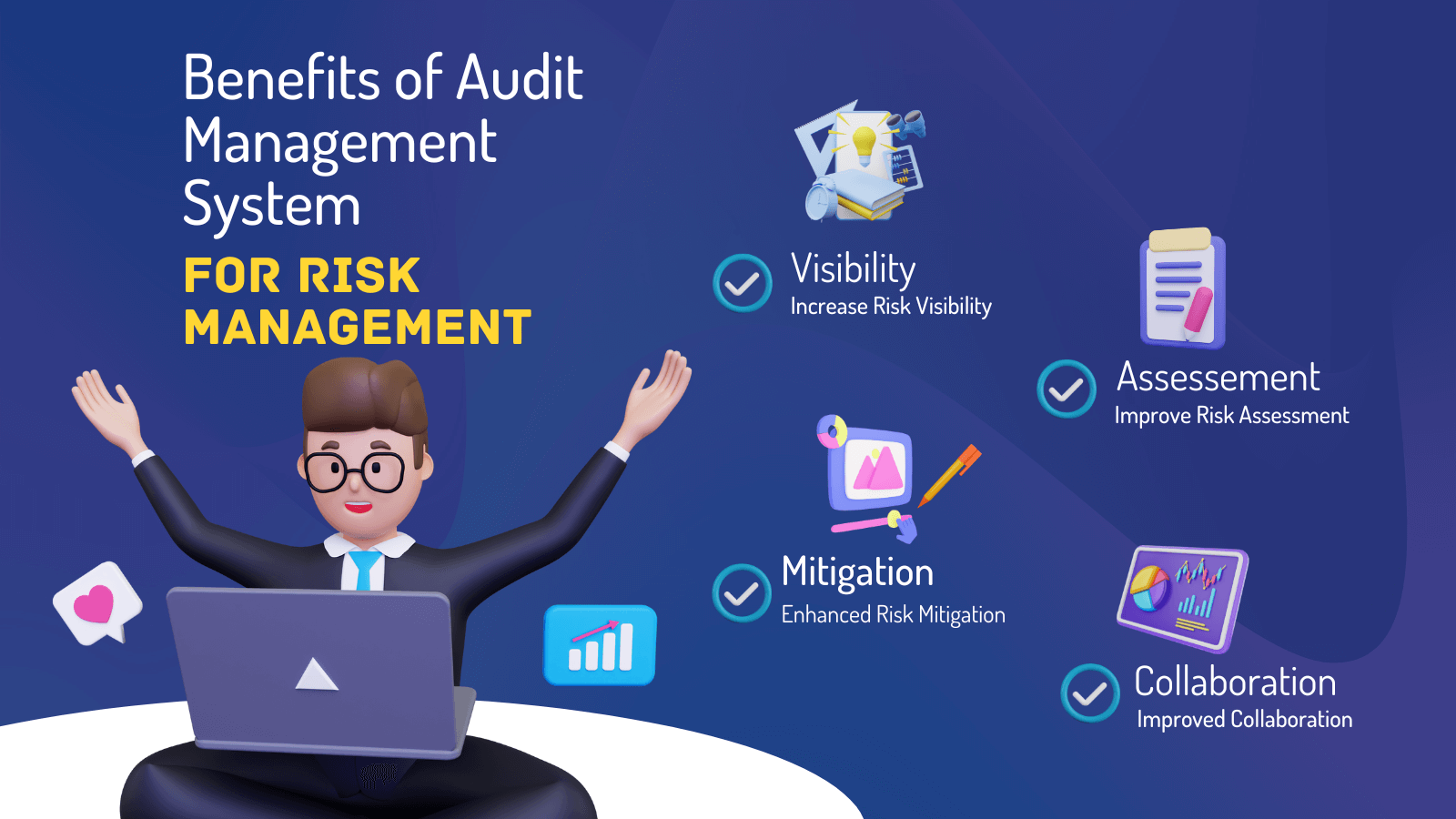
In this blog, we will dive into the world of ERM software application, discovering what it is, its advantages, attributes, and so on so that you can build one for your company. Enterprise Risk Management (ERM) software is the application program for preparation, routing, arranging, and managing company activities and simplifying threat monitoring procedures.
With ERM, companies can make insightful decisions to improve the overall durability of the business. Devoted ERM systems are vital for companies that regularly deal with large amounts of sensitive information and multiple stakeholders to authorize strategic choices.
It can be prevented by making use of the ERM software application system. This system automates guideline compliance management to keep the organization protected and compliant.
All about Risk Management Enterprise
You can also attach existing software program systems to the ERM via APIs or by including data by hand. Services can make use of ERM to review dangers based upon their prospective influence for better danger administration and mitigation.: Including this function enables customers to get real-time notifications on their tools about any kind of risk that might take place and its effect.
Instead, the software application permits them to set thresholds for different processes and send out press alerts in case of feasible threats.: By incorporating information visualization and reporting in the personalized ERM software application, companies can acquire clear insights about risk fads and performance.: It is required for companies to comply with industry compliance and regulatory requirements.
These platforms enable firms to implement best-practice danger administration procedures that align with sector requirements, using a powerful, technology-driven method to recognizing, assessing, and mitigating risks. This blog explores the benefits of automatic risk management tools, the locations of risk monitoring they can automate, and the worth they give a company.
Rumored Buzz on Risk Management Enterprise
Teams can establish forms with the appropriate fields and easily produce different forms for different risk types. These danger assessment forms can be circulated for conclusion through automated operations that send notices to the pertinent team to complete the types online. If types are not finished by the target date, then chaser e-mails are automatically sent by the system.
The control monitoring and control testing procedure can also be automated. Firms can make use of automated workflows to send routine control examination notifications and personnel can go into the results via online types. Controls can also be monitored by the software program by establishing guidelines to send alerts based upon control data kept in other systems and spread sheets that is pulled right into the platform through API integrations.
Danger monitoring automation software can also sustain with threat reporting for all levels of the venture. Leaders can check out reports on danger exposure and control effectiveness with a selection of reporting outputs consisting of fixed records, Power BI interactive reports, bowtie evaluation, and Monte Carlo simulations. The capacity to pull genuine time records at the touch of a switch eliminates difficult information manipulation tasks leaving risk teams with even more time to analyze the data and encourage the business on the most effective training course of activity.
Organizations operating in competitive, fast-changing markets can not pay for delays or ineffectiveness in addressing prospective dangers. Typical threat management utilizing hands-on spreadsheet-based procedures, while acquainted, usually lead to fragmented information, taxing coverage, and a raised chance of human mistake.
Not known Facts About Risk Management Enterprise
This ensures threat registers are always existing and straightened with organizational purposes. Compliance is one more vital vehicle driver for automating threat monitoring. Standards like ISO 31000, CPS 230 and COSO all give assistance around risk administration ideal methods and control structures, and automated danger monitoring devices are structured to align with these demands helping find more companies to satisfy most typically utilized danger monitoring requirements.
Seek threat software systems with an authorizations power structure to easily set up operations for threat rise. This performance enables you to tailor the view for every user, so they just see the data pertinent to them. Ensure the ERM software offers individual tracking so you can see that entered what data and when.
Seek out devices that offer project threat administration capabilities to try this website handle your projects and profiles and the associated risks. The benefits of embracing danger administration automation software application extend much beyond effectiveness.

The 5-Second Trick For Risk Management Enterprise
While the situation for automation is compelling, applying a threat monitoring platform is not without its challenges. For one, data high quality is important. Automated systems count on precise, up-to-date info to supply purposeful insights. To get rid of the obstacles of risk management automation, organizations should buy data cleaning and governance to make sure a strong structure for executing an automated platform.
Automation in risk management encourages businesses to change their approach to risk and develop a more powerful foundation for the future (Risk Management Enterprise). The inquiry is no longer whether to automate risk management, it's how quickly you can start. To see the Riskonnect in action,
The response typically hinges on how well risks are prepared for and taken care of. Job management software application acts as the navigator in the troubled waters of project implementation, offering devices that determine and assess threats and design approaches to alleviate them effectively. From real-time data analytics to extensive threat tracking dashboards, these devices provide a 360-degree view of the job landscape, allowing job supervisors to make enlightened choices that keep their tasks on my response the right track and within budget plan.